Lenovo Products and the “Superfish” Vulnerability
You may have seen reports in the media recently about something called “Superfish” on Lenovo laptops. Before I go into details, I want to stress one thing:
According to a statement from Lenovo, “ThinkPad, ThinkCentre, Lenovo Desktop, ThinkStation, ThinkServer and System x products are not impacted.” This includes all Lenovo products sold by GC Support as well as products I have recommended customers buy through Shack West Pty. Ltd.
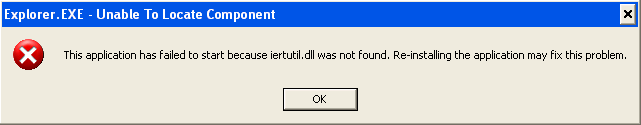
This is a very serious vulnerability which can allow an attacker to intercept information that should be completely secure on secure websites. By this I mean websites that use an address starting with “HTTPS://” including online banking and sites accepting payment information such as credit card info.
The “Superfish” software, is intended to monitor your web browsing activity and use the information to “recommend” products similar to what you’re viewing. To say the least, including such software pre-installed on systems was a very poor decision on Lenovo’s part. This kind of software is often politely called “Potentially Unwanted Programs” or “PUPs”. Less politely it might even be called malware, adware or spyware. Lenovo has stated that they have taken measures to disable the software and provided removal instructions. They’ve also said that they have stopped installing it on all new units.
The problem is that the “bad guys” have worked out how to use the software to trick users into thinking they are talking to a secure site, all the while being able to see information that should be secure. They could potentially use this in a number of ways, including collecting details such as online banking passwords and details, or tricking you into installing more unwanted programs by making them look like they’re coming from a trusted source. Lenovo’s “deactivation” steps do not protect against these things unless users also remove the program from their systems.
Here are the essential links to information you might need if you are concerned about this issue:
Lenovo Security Advisory LEN-2015-010 – “SUPERFISH VULNERABILITY” (Includes a list of affected models.)
Lenovo “SUPERFISH UNINSTALL INSTRUCTIONS”
Note that just uninstalling from the Control Panel does NOT resolve the security threat. You must also manually remove the compromised certificate. The above link shows how.
If you have any concerns that you might be impacted by this issue, or any other security issue on your systems, please contact me for advice.
Note that this post represents my best understanding of this issue based in information provided by Lenovo and other sources. It is opinion only. No guarantees are offered or provided. Further information may reveal additional impacts and risks in the future.
GC
 UPDATE: Since I wrote this Apple have changed the name of the iPad in question to the “iPad with WiFi + Cellular” in many markets including Australia. This solves the problem neatly and reduces the following article to historical interest only.
UPDATE: Since I wrote this Apple have changed the name of the iPad in question to the “iPad with WiFi + Cellular” in many markets including Australia. This solves the problem neatly and reduces the following article to historical interest only.